Ann Cavoukian has long touted the benefits of “data privacy by design” and now the European Union has passed an overarching privacy law called the General Data Protection Regulation, which embeds that requirement.
 The regulation comes into effect in 2018 in the EU. What is unusual about the regulation is that it applies to all EU member countries, replacing the separate privacy laws of each of its 28 countries.
The regulation comes into effect in 2018 in the EU. What is unusual about the regulation is that it applies to all EU member countries, replacing the separate privacy laws of each of its 28 countries.
Privacy by design was first developed by Cavoukian in the 1990s when she was privacy commissioner of Ontario. It is an approach to protecting privacy by embedding it into the design specifications of technologies, business practices, and physical infrastructures.
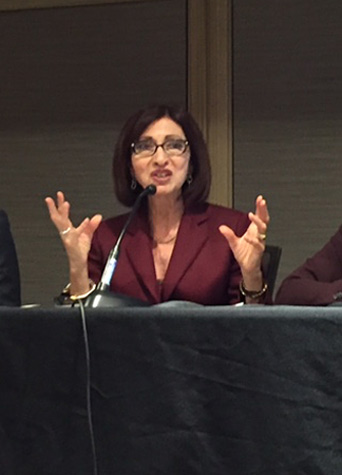
“That in itself is huge,” said Cavoukian, now the executive director of the Privacy and Big Data Institute at Ryerson University.
She was speaking on an International Association of Privacy Professionals panel last week in Toronto called “Privacy by design: How I learned to stop worrying and love disruptive technology.”
Even though privacy by design has been embraced globally for many years, the EU law is the first time it’s appearing in a statute.
Cavoukian noted that Canada’s privacy commissioner, Daniel Therrien, is also now asking if privacy by design should be embedded into Canadian law.
“Keep your eyes open for this, and if you lead by privacy by design it will be more likely you will be compliant with the GDPR and you will be more likely to be meeting the requirements of many jurisdictions because privacy by design raises the bar considerably,” she said.
Abigail Dubiniecki, legal counsel for the Canadian Air Transport Security Authority, noted that even if an organization doesn’t have operations in the EU, if it is directing services to EU residents, it can still be captured by the requirements.
With distrust of how organizations are handling personal data at an all time high, how can organizations foster trust with customers in the private and public sector?
“You have to find ways to grow trust,” said Cavoukian. “When I was privacy commissioner I told businesses to treat privacy as a business issue — focus on the tech and how you can increase privacy thereby increasing trust and be compliant with the legislation.”
Cavoukian said with the Internet of Things exploding at such a rapid pace, if companies took time to reflect on the protections that could be embedded from the outset, they would be much further ahead. Companies are still too siloed though to make sure it happens at the design stage
“When I talk to software designers and ask why they aren’t embedding privacy into the design of their technology they say, ‘We’d love to do that but the instructions we receive don’t reflect the need to do that.’ They say if we had the instructions at the front end, it’s easy to do,” she said.
She referred to the “risk intelligence approach” which anticipates risk and identifying them upfront in an effort to mitigate risk by incorporating privacy into design.
Dubiniecki said some view the problem as a generational gap — that some older age groups are more concerned about privacy than others that have “softer” security concerns.
“There is the idea that some will sacrifice privacy for personalization,” she said. “They want something customized to their needs so some innovators see privacy as a barrier to innovation but others see it as an opportunity.”
Cavoukian agreed it is an opportunity. She says people often see privacy as an impediment but in fact she says “privacy breeds innovation.”
“If you can embed privacy from the get go it will assure customers and keep regulators out of your door because you will be building it in in the strongest way possible.”
Protection of data should also be the top concern of any organization, she said.
“In this day and age of cyber attacks, if you don’t have data protection end to end you won’t have privacy. You have to have secure data collection and through the secure destruction of the data,” she said.
“Remember, it’s not your data — just because you have custody and control of it because you collected it doesn’t mean it belongs to you — it belongs to the data subject.”




